Defend against the #1 initial access vector
Social engineering is the leading cause of enterprise breaches. SlashID stops impersonation attacks with cryptographic identity verification that’s faster, cheaper, and less invasive than scanning faces or checking IDs.
Social engineering accounted for over a third of all incident response cases in the past year — more than any other initial access vector. Vishing, deepfake impersonation, and help desk manipulation bypass MFA, exploit human trust, and give attackers a foothold in minutes.
Traditional defenses don’t scale: security awareness training can’t keep up with AI-generated deepfakes, and face-scanning identity verification is expensive, invasive, and impractical to roll out broadly. SlashID’s Mutual TOTP takes a different approach — lightweight cryptographic proof of identity for both parties in any interaction, deployed on any device, with no biometric data stored and no hardware tokens required.
Verify both sides
Mutual TOTP proves both parties’ identities simultaneously with device-bound cryptographic codes. Attackers can’t fake one side — even with cloned voices, stolen credentials, or deepfake video.
Faster and cheaper than identity verification
No face scanning, no ID checks, no liveness detection, no biometric data stored on third-party servers. Deploys in hours and costs a fraction of traditional identity verification.
Respond with full risk context
Every verification request is correlated against SlashID’s identity graph. High-risk identities trigger different workflows than low-risk users.
Benefits
How it helps
Mutual verification, not one-way
Both parties prove their identity simultaneously using device-bound TOTP codes that refresh every 30 seconds. Attackers can’t fake one side of the handshake — even with cloned voices, compromised credentials, or deepfake video. Partial verification triggers a warning.
Beyond the help desk
Not just call-center protection. Mutual TOTP works for any human-to-human interaction where identity matters: employee-to-employee calls, executive wire-transfer approvals, vendor onboarding, contractor access requests, remote worker check-ins.
Desktop and mobile with biometric protection
Available on both platforms with Face ID and Touch ID. No additional hardware tokens, no awkward video-verification workflows, no biometric data stored on third-party servers.
Faster to deploy, cheaper to run
No face scanning. No liveness detection. No identity document processing. Mutual TOTP deploys in hours, not weeks, and costs a fraction of traditional identity verification tools — because if employees don’t actually use it, it doesn’t matter how secure it is.
Identity risk context for smarter remediation
Every verification request is correlated against SlashID’s full identity risk profile and access graph context. A password reset request from a high-risk identity triggers escalation; the same request from a low-risk user proceeds normally.
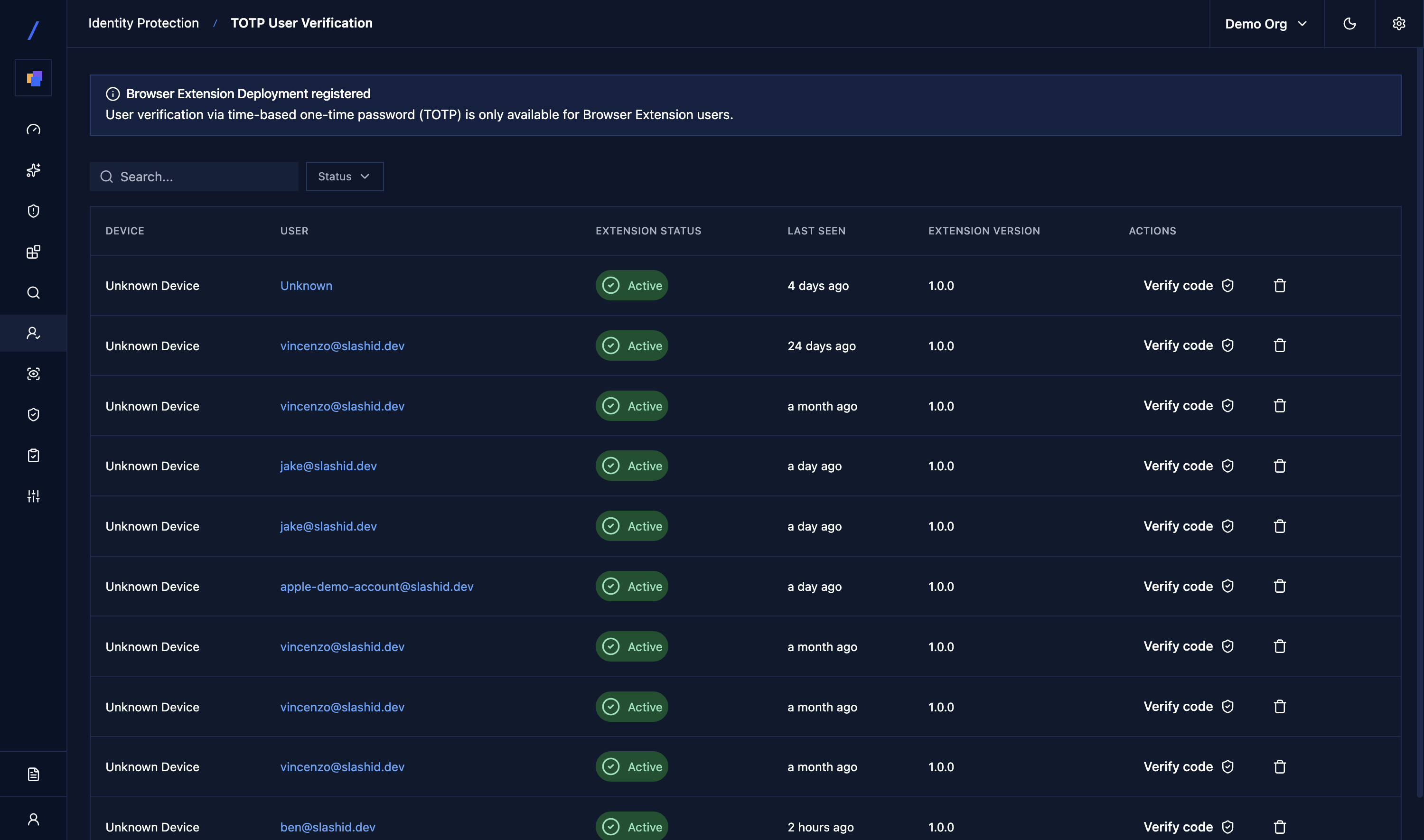
Full audit trail
Every verification session logged with initiator, target, timestamp, verification status, and outcome — ready for compliance reporting and incident investigation.
Easy to deploy
How it works
Employees activate the app with a token from IT. Biometric protection (Face ID / Touch ID) secures access on the device.
Either party starts a verification handshake via email address lookup. No phone numbers or external directories needed.
Both parties receive a unique 6-digit TOTP code. Each reads their code aloud; the handshake succeeds only when both codes are confirmed.
The verification outcome feeds into SlashID’s identity graph. Requests from high-risk identities or anomalous patterns escalate automatically.
Unique Product Core
Mutual TOTP Engine
- RFC 6238 TOTP codes bound to device and timestamp
- Bidirectional verification flow with real-time session synchronization
- Biometric-protected activation
- Impossible to guess, replay, or forge
Identity Risk Correlation
- Verification events correlated against the full access graph and identity risk profile
- High-risk requests escalate automatically
- Complete audit trail for every session — initiator, target, timestamp, status, outcome
How the MGM and Caesars breaches started with a phone call, and what they reveal about defending against identity-driven attacks.