Govern every AI identity touching corporate data — without agents
The first access graph-native solution built to govern OAuth-connected AI applications, autonomous agents, and MCP servers. Agentless visibility and policy enforcement across every AI tool your workforce uses.
Every time an employee authorizes a new AI assistant, connects an MCP server, or hands a task to an autonomous agent, they create a new non-human identity with access to corporate resources.
Traditional governance platforms cannot keep pace with AI tools that are installed in seconds, inherit broad OAuth scopes, and connect further downstream via MCP and agent frameworks. SlashID's AI Identity Governance brings these identities under the same visibility, access control, and lifecycle policies enterprises already apply to users and service accounts — with zero endpoint software required.
Unified AI identity visibility
Continuous discovery of OAuth 2.0 grants issued to AI applications, MCP servers, shadow AI usage, and models hosted on Amazon Bedrock, Azure OpenAI, and equivalent CSP-native services. See not just that a user connected to an AI app, but exactly which mailboxes, drives, calendars, or repositories that app can reach.
Policy-based access control
Allow, restrict, or disable access to specific AI applications, model providers, or agentic identities using any attribute in the graph. Define rules once and enforce them continuously across the joiner-mover-leaver lifecycle, with a full audit trail.
Continuous SoD enforcement
Express toxic combinations as saved Access Graph queries — for instance, identities with access to regulated customer data that also hold active grants to external LLMs — and automatically trigger remediation workflows against every identity returned.
Benefits
Why agentless AI governance
Zero endpoint footprint
No agents, no proxies, no inline inspection. SlashID leverages pre-tool-use hooks, real-time OpenTelemetry export, and vendor admin APIs to achieve full visibility without deploying endpoint software — covering Claude Code, Cursor, Gemini CLI, GitHub Copilot, Microsoft 365 Copilot, and ChatGPT.
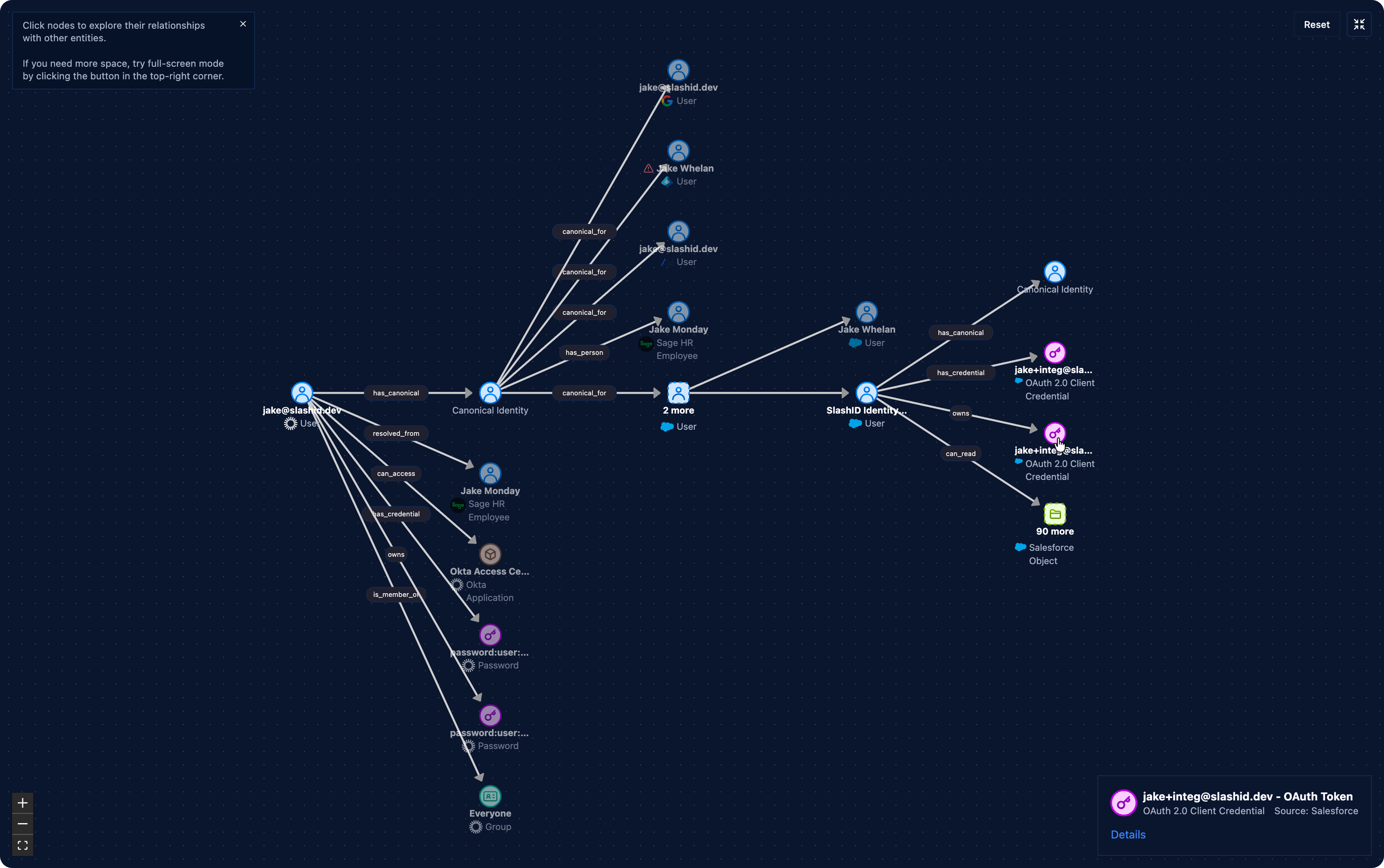
OAuth scope visibility as graph edges
The Access Graph models OAuth scopes as first-class edges, so security teams can see not just that a user connected to an AI app, but exactly which mailboxes, drives, calendars, or repositories that app can reach — and which identities can reach them through it.
MCP server governance
Discover every MCP server configured across your fleet — user-level and project-level — through settings-file hooks and telemetry. Detect unapproved servers, catalog credentials at rest, and enforce allowlists without intercepting traffic.
Shadow AI detection
Surface unauthorized AI tool usage through the SlashID Browser Extension and identity graph correlation. Identify consumer AI tools accessing corporate data before they become the next breach vector — like the OAuth-based attack in the April 2026 Vercel incident.
Lifecycle automation for AI identities
Apply the same joiner-mover-leaver policies to AI identities as human users. When an employee changes roles, their AI tool authorizations are automatically reviewed. When they depart, OAuth grants and MCP server access are revoked.
Compliance-ready audit trail
Every AI tool authorization, policy decision, and remediation action is logged with full context. Generate audit-ready reports for SOC 2, ISO 27001, HIPAA, and custom frameworks on demand — with the same primitives used for SaaS and cloud entitlements.
Agentless deployment
How it works
Read-only connectors and pre-tool-use hooks discover OAuth grants to AI applications, MCP server configurations, and model provider access — no endpoint agent required.
The Access Graph maps every AI identity, the OAuth scopes it holds, the resources it can reach, and the human identities that authorized it — continuously and automatically.
Define policies once using any graph attribute. Prevent HR or finance personnel from authorizing consumer AI tools, restrict MCP server access by department, or block toxic combinations in real time.
Automatically trigger revocation, MFA step-up, ticket creation, or Slack notification when policy violations are detected. Schedule continuous segregation-of-duties checks against the full identity population.
Unique Product Core
Access Graph Engine
- OAuth scopes modeled as first-class graph edges
- MCP server and AI agent discovery across the fleet
- Unified view of human, non-human, and agentic identities
- Saved queries for continuous SoD monitoring
Agentless AI Controls
- Pre-tool-use hooks for Claude Code, Cursor, Gemini CLI, and GitHub Copilot
- OpenTelemetry integration for real-time tool-call visibility
- Vendor API polling for Microsoft 365 Copilot and ChatGPT Enterprise
- Policy-based lifecycle automation across the joiner-mover-leaver cycle