Blog
Security
/ 1 Jun, 2026Analysis of the 2026 Stryker Breach: Weaponizing Cloud Endpoint Management
On March 11, 2026, attackers turned Stryker Corporation's own Microsoft Intune device-management plane into a non-encrypting wiper, factory-resetting roughly 200,000 endpoints across 79 offices worldwide without dropping a single piece of custom malware.
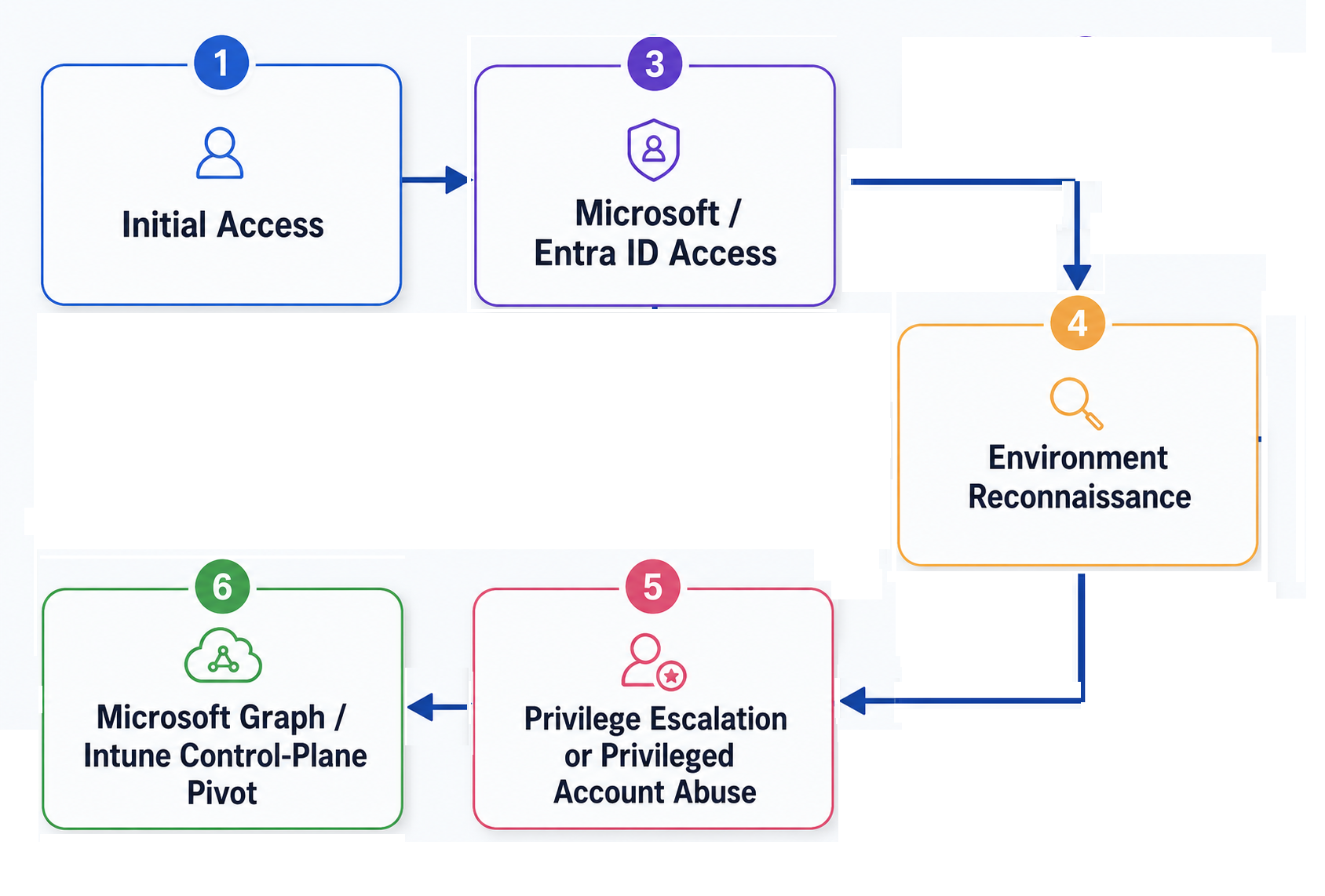
This analysis reconstructs the Living-off-the-Land attack chain — from infostealer logs and AiTM session theft through privilege escalation to the Intune control-plane pivot — and shows how SlashID's MITM/AiTM detection, phishing-resistant authentication, behavioral anomaly detection, and just-in-time privileged access stop it.
Security
/ 1 Jun, 2026Analysis of the 2026 Stryker Breach: Weaponizing Cloud Endpoint Management
On March 11, 2026, attackers turned Stryker Corporation's own Microsoft Intune device-management plane into a non-encrypting wiper, factory-resetting roughly 200,000 endpoints across 79 offices worldwide without dropping a single piece of custom malware.
This analysis reconstructs the Living-off-the-Land attack chain — from infostealer logs and AiTM session theft through privilege escalation to the Intune control-plane pivot — and shows how SlashID's MITM/AiTM detection, phishing-resistant authentication, behavioral anomaly detection, and just-in-time privileged access stop it.


Security
/ 20 Apr, 2026Vercel April 2026 Security Incident: How a Compromised OAuth App Led to a Major Breach
On April 19, 2026, Vercel disclosed that attackers compromised an employee's Google Workspace account through a malicious OAuth 2.0 application originating from Context.ai, a third-party AI tool.
This post breaks down how the attack worked, what OAuth scopes were abused, and how organizations can detect and respond to these threats with and without SlashID.


Security
/ 30 Mar, 2026Deepfake Impersonation Attacks (Part 2): Defending with SlashID Mutual TOTP
As generative AI makes deepfake impersonation attacks increasingly convincing, traditional enterprise security controls fail to protect human-to-human communication channels.
This post introduces SlashID Mutual TOTP, a cryptographic verification mechanism that replaces perception-based trust with mathematical proof of identity, stopping deepfake impersonation attacks before sensitive information is shared.


Security
/ 16 Mar, 2026Deepfake Impersonation Attacks (Part 1): Anatomy of Modern Deepfakes
In 2024, Arup, a global engineering consultancy, fell victim to one of the most sophisticated deepfake fraud attacks, losing $25 million after an employee joined what appeared to be a legitimate video conference with AI-generated deepfake executives.
This post explores the technical evolution of deepfake technology, from early GANs to modern diffusion models, and explains how attackers can now bypass enterprise liveness detection to impersonate executives in real-time video calls.


Security
/ 6 Mar, 2026NYDFS 2026 Vishing Advisory: Detection and Defense with SlashID
On February 6, 2026, NYDFS issued an industry letter warning DFS-regulated entities about a spike in targeted vishing attacks where threat actors impersonate IT help desk staff to steal credentials and MFA codes.
This post breaks down the technical mechanics of the campaign, why it reliably bypasses MFA, and how to detect and contain it using identity telemetry with SlashID Identity Protection, Mutual TOTP verification, and MITM detection.


Security
/ 16 Jan, 2026Scattered Spider Tradecraft: Identity Abuse, Attack Flow, and Defense
Scattered Spider is a highly adaptive cybercrime group that breaches enterprises by abusing identity, trust, and legitimate access paths rather than malware exploits.
Learn about their identity-centric attack flow, real-world campaigns like the MGM and Caesars breaches, and how to defend against these sophisticated threats.


Security
/ 9 Nov, 2025Microsoft Actor Token Forgery
Actor Token Forgery is one of the many techniques adopted by attackers to escalate privileges and move laterally via identity vector.
This post reconstructs the attack flow, maps it to MITRE ATT&CK, and outlines immediate detection and defense actions.


Security
/ 21 Sep, 2025Access tokens strike again, the Salesloft Drift breach
In mid‑August 2025, GTIG confirmed a large‑scale credential‑harvesting and data‑theft campaign abusing trusted OAuth integrations (Drift) to access Salesforce orgs.
Attackers (UNC6395) used stolen Drift OAuth tokens to mass‑query Salesforce, mine embedded secrets (AWS, Snowflake), and pivot into connected platforms.
This post reconstructs the attack flow, maps it to MITRE ATT&CK, and outlines immediate detection and defense actions.


Security
/ 31 Aug, 2025Illicit Consent-Granting & App Backdooring – Obtaining persistence in Entra
Attackers are increasingly targeting Entra ID by silently injecting high-privilege OAuth grants and backdooring enterprise apps—achieving persistence without user interaction.
This blog provides a technical deep dive into the full attack lifecycle - initial access, consent injection, privilege escalation, and evasion.
We map each stage to MITRE ATT&CK, show real-world Graph API and CLI techniques, and outline concrete detection signals and hardening practices for defenders.


New Feature
/ 5 May, 2025Achieving Least Privilege: Unused Entitlement Removal
Unused entitlements are one of the easiest ways for an attacker to move laterally in a target environment.
However, reducing permissions is often very difficult due to availability concerns and the complexity of the permission systems.
This blog post explores how SlashID solves this problem so that customers can automatically resize identity permissions and
achieve least privilege.



